What would you do if rockets were striking your country? RT if you agree that #Israel has the right to self-defense. http://t.co/OvnPKErQ
— Israel Defense Forces (@IDF) November 16, 2012
Last Wednesday and Thursday, I attended the inaugural Social Media in Defence Forum held by Australian Defence Magazine, so it’s only fitting that I report back with a blog post.
There was a variety of informative presentations by both Australian and international speakers (Defence Department or defence-related industry) on their experiences with social media, best practice and the risks and resources associated with Defence’s use. In recognition of the ubiquity of social media in the workplace and the difficulty of trying to regulate its use, one speaker even remarked that his company had reduced a 30-page social media policy to merely three words: ‘empower and trust’. It’s a cool way of dealing with new media (though I’m sure it’s coupled with other kinds of guidance) and reflective of industry’s ability to respond in a more agile way.
But this is a scary space for organisations used to controlling information. Defence is, as they say, ‘a different beast’, subject to different constraints and lagging bureaucratic processes. So at the Forum, I wanted to present a case study that investigated how a military could overcome some of the usual objections and cautions related to more active social media use. The most stunning example of late has been Israel and Hamas’ ‘Twitter war’, so I talked about the use of social media by the Israel Defense Forces (IDF) and Al-Qassam Brigades (Hamas’ military wing) and the implications of social media for warfare.
It’s a case where both sides were as active on social media as on the battlefield. The IDF used Twitter to announce both the commencement of Operation Pillar of Defense—aimed to stem Gazan rockets falling into Israel—on 14 November and the assassination of Hamas leader Ahmed Jabari.
Ahmed Jabari: Eliminated. pic.twitter.com/sCnQnKkM
— Israel Defense Forces (@IDF) November 14, 2012
In response, the Al-Qassam Brigades launched Operation Shale Stones via Twitter. @IDFSpokesperson and @AlqassamBrigade continued tweet by tweet in the virtual realm while violence erupted in the physical. For instance, here:
https://twitter.com/AlqassamBrigade/status/268791630583193600
and here:
https://twitter.com/AlqassamBrigade/status/272094326354477056
What’s notable about the use of social media in this instance isn’t just the translation of violence into a more frivolous form, depicted and conveyed by movie-style posters and retro-looking artwork like the rockets picture above. That happens with traditional media as well. The significance is the way in which other parties can become embroiled in online hostilities, which can lead to serious escalation and complex legal questions (or so it seems to we non-lawyers, anyway).
The risks of escalation are real. In this case, Israel propagated an aggressive and synchronised social media campaign as befits a professional military. But asymmetry on the battlefield can also play out in cyber space, and vigilantes can buy in. As my Land Warfare Studies Centre colleague, Clint Arizmendi, points out, a range of non-state cyber actors can join the fray, backing the underdog and influencing the ‘battlespace’. In the IDF-Hamas conflict, hacktivist group Anonymous, in its support for the Palestinians, declared cyber war on Israel; it claimed to have taken down some 650 Israeli websites. In a conflict that, at some points, appeared to have three (and more) actors, could Anonymous have been considered a ‘combatant’? Can social media bystanders who participate in cyber attacks be deemed ‘legitimate targets’? At the conference, one audience member suggested during question time that the Geneva Convention might even apply.
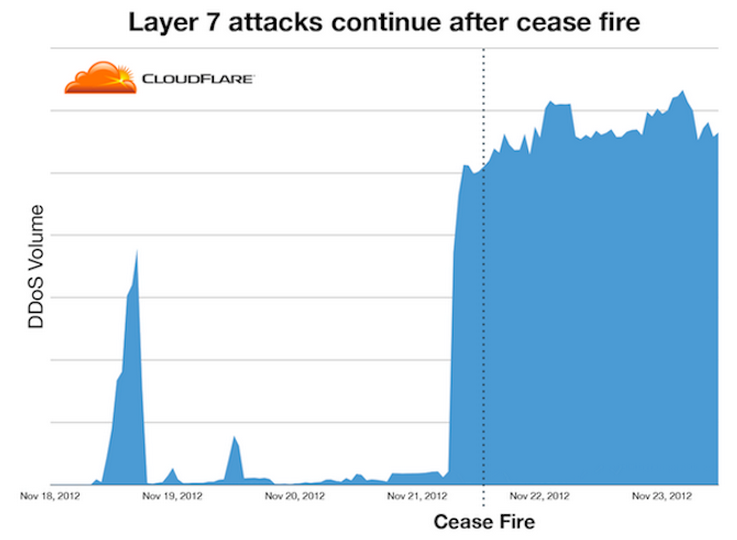
While Anonymous formally acknowledged the 21 November ceasefire, hostilities in the form of cyber attacks continued against both Israel and Hamas websites. CloudFare, an American company that provides cyber protection services, noted a significant spike in distributed denial of service attacks after the ceasefire was announced (see graph below). It raises the prospect of negotiating an online ceasefire to accompany a physical one. (h/t Chloe Diggins @ LWSC for this point)
Lastly, there seemed to be confusion on behalf of social media companies as to how to handle the IDF-Hamas case. As some commentators observed, the IDF’s early tweet-threats violate ‘The Twitter Rules’ on violence and threats. Yet the tweet has remained. Likewise, Hamas, a designated Foreign Terrorist Organization under US law, has been allowed to continue operating on the social media platform—this seemingly violates Twitter’s Terms of Service as well. YouTube has wavered in its approach to this recent conflict, removing the IDF video of Jabari’s assassination (below) shortly after its posting, only to reinstate it not long after.
This doesn’t mean there aren’t answers for some of the questions raised by the IDF-Hamas case. It means we’re still working out how social media fits into warfare and what the legalities are. There are other questions too, like how effective these social media campaigns really were. Companies might use online tools like Google Analytics or Klout to determine their level of ‘influence’, but in the midst of a war, it’s really not that clear cut. Israel and Hamas both used social media to further strategic messaging—to deflect criticism of civilian casualties or to boast the efficacy of systems like Iron Dome—but measuring its contribution to the overall strategic outcomes is another matter.
In any case, trying to measure this kind social media activity might not matter too much—the overheads of using civilian social media platforms probably aren’t very onerous. So I suspect that we’re going to see more of this activity. And it will challenge militaries as they strive to increase the benefits of social media in selling their messages while limiting its ability to embarrass or compromise them.
Natalie Sambhi is an analyst at ASPI and editor of The Strategist.

