With the heightened threats in cyberspace, the Australian government wishes to hasten the passage of crucial amendments to the Security of Critical Infrastructure Act 2018.
The unannounced information war with China has put tremendous strain on the Five Eyes intelligence-gathering alliance in Oceania. The relentless compromising of the private sector, which remains a soft but strategic target, has diluted the conventional boundaries of conflict, forcing the government to enhance its legislative reach.
The Security Legislation Amendment (Critical Infrastructure) Bill 2020 substantially expands the definition of critical infrastructure, acknowledging the complex web of interdependencies which fuels the internet. It also charts the contours of a ‘sovereign Australian cyberspace’ crisscrossing the porous boundaries of government and civilian networks.
The bill proposes enhanced security obligations for critical industries against cyber threats and defines thresholds at which the government’s signals intelligence apparatus may need to step in.
While the contentious issue of how much access into the enterprise networks the Australian Signals Directorate should be offered requires deliberation, the private sector can’t withstand the Category 5 hurricane that a state-sponsored cyberattack could be.
Having led a similar effort in India in 2009—culminating in the creation of a constitutional body called the National Critical Information Infrastructure Protection Centre—I’d urge the Australian government to challenge the precedents.
Terms like ‘critical infrastructure’ could be mere lexical trappings from the policy past. That one was introduced in US President Bill Clinton’s 1996 Executive Order 13010. In 1998, the concept was updated to include the cybersphere. The US government networks were penetrated by teenagers that year, and a National Security Agency simulation exercise to test network vulnerabilities disrupted national services.
As the US establishment grappled with this esoteric domain, ‘Cyber Pearl Harbor’ came to denote the impending catastrophe delivered by a foreign adversary that would bring the nation to its knees. It’s strange and amusing to see that the rhetoric hasn’t changed in two decades. We base our response thresholds on the same imagined parameters of digital cataclysms.
But the reality could be far more nuanced and the threat even more insidious.
Veteran cybersecurity analysts Andrew Burt and Daniel Geer say that something becomes critical infrastructure when it is adopted by society. ‘Adoption is the gateway drug to criticality. When enough people depend on something in cyberspace, that something is made critical.’
The idea of criticality underlines a cognitive dependency on technologies and systems that society takes for granted—not just power grids.
When a comedy movie portrayed him unflatteringly, an incensed North Korean dictator Kim Jong-un ordered the hacking of Sony Pictures in 2012. US President Barack Obama vowed to deliver a ‘proportional response’ against the targeting of, well, an American film studio—a far cry from the usual definition of critical infrastructure.
The attack was perceived as a threat to freedom of speech, which was considered more crucial than critical infrastructure. The incident had an inescapable cognitive angle and ignoring it could have set unfavourable thresholds of cyber escalation for the US.
Similarly, the 2016 hack of the Democratic National Convention—whose ripple effects on American democracy are still being felt—never really fitted into the Pentagon’s definition of a cyberattack. The generals mostly imagine it within the effects-based spectrum of ‘destroy, deny, degrade’—blowing stuff up. It was an out-and-out cognitive operation.
Before and after Russia’s 2014 annexation of Crimea, the Ukrainian power grid was repeatedly targeted with destructive malware. Ben Buchanan notes in his book The hacker and the state, ‘It plunged hundreds of thousands of people into darkness … but did not devastate cities or starve populations.’ Life went on. But the attacks did demotivate the population, affecting people’s will to fight and resist the Russian insurgency.
The lights may not go out, but the democratic core of a nation could be sabotaged right under their glare.
Many cyber capabilities and effects manifest in the cognitive rather than the kinetic or physical dimensions. Those in the cognitive dimension not only challenge operational assumptions but also call into question generalisations about critical infrastructure, the thresholds of conflict and deterrence.
Damian Tambini of the London School of Economics writes: ‘Information warfare is, par excellence, a challenge by authoritarian states to the vulnerabilities of democratic states. It is an attack on open society and liberalism per se.’
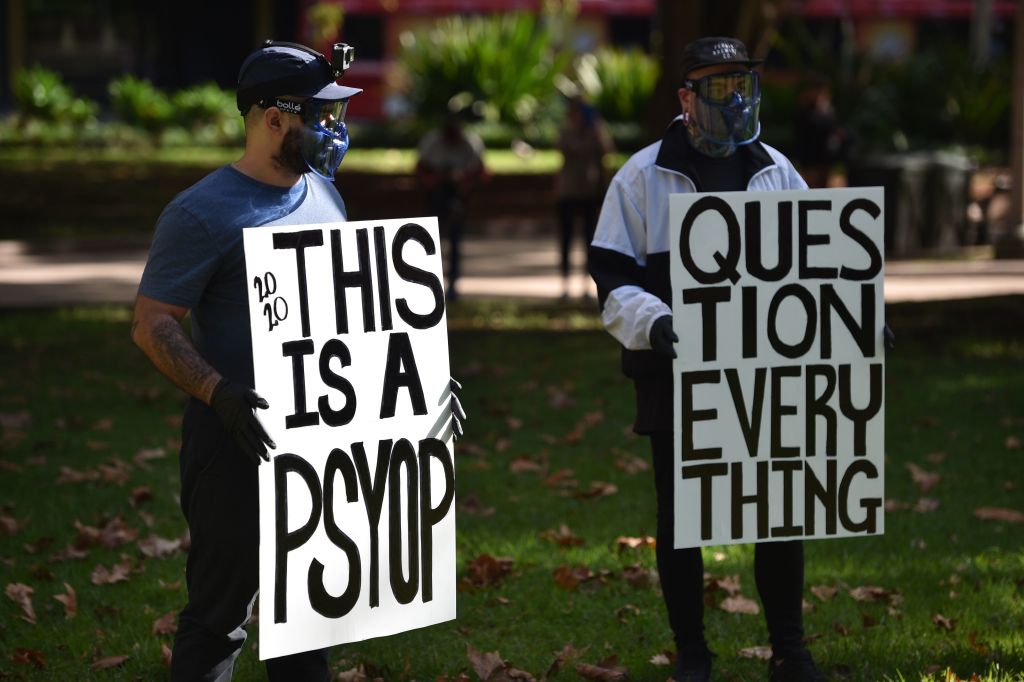
Recently, an Australian news channel was censured for spreading medical misinformation as protesters flouted Sydney’s Covid-19 lockdown rules.
In the raging pandemic, the impacts of computational propaganda amplifying harebrained theories on vaccinations are being felt globally. Conspiracy theorists, tribalists and populists are now knocking at the corridors of power in liberal democracies.
The playbooks for agitational social movements existing on the margins of society and foreign information operations do closely align.
Adversaries are experimenting with information warfare to erode liberal democracy. The aim of doctrinal concepts like Russia’s ‘reflexive control’ and China’s ‘three warfares’ is to corrupt other nations’ epistemic foundations. They hit the democratic state at the most delicate point: its institutional relationship with truth and objectivity.
Unlike conventional war, an informational conflict starts unannounced and thrives in a ‘grey zone’ between war and peace. The idea is to achieve a victory without a physical conflict by making the strategic conditions favourable to the foreign adversary in a sustained information confrontation.
Keir Giles of Chatham House feels that Russia’s new approach to war is simply a recognition of the ‘primacy of the political over the military’, so much so that military strength could become irrelevant. In that sense, through its interference in the US 2016 election, Russia may have bagged a resounding victory in the US information space by achieving the most hallowed objective: regime destabilisation.
The US Senate Intelligence Committee Chair shared a grim prophecy in 2017 that Russia wanted ‘both sides to battle in the streets’. The January 2021 siege of the US Capitol by militant conspiracy theorists was just that battle.
Capturing the essence of disinformation, Corneliu Bjola and Krysianna Papadakis from Oxford University write: ‘[Its aim is] not primarily to alter people’s views in support of certain policies, but to induce them into a state of self-defeating and endemic scepticism by undermining the very criteria on the basis of which they develop their cognitive abilities to make sense, interpret, shape reality.’
Dissent, the essential lubricant of a democracy, can be weaponised in the hyperpluralism of social media.
Militaries of Western democracies have had a very strict mandate when it comes to information operations. Propaganda has generally been limited to specific theatres of conflict in a very tactical way and counterpropaganda remains off limits due to the risk of influencing the domestic populace. The political leadership, too, has struggled with a clear articulation of the threat.
Battling disinformation with a clampdown, censorship or by resorting to less liberal positions gives an adversary the upper hand.
Bjola and Papadakis studied the Finnish resilience to computational propaganda orchestrated by Russia. They concluded that while Finland was as susceptible to emotive issues as any other democracy, it had managed to create a set of checks and balances across the government, civil society and traditional media to reinforce truth and objectivity. Their takeaway is that ‘a society is only as resilient to disinformation as its most vulnerable segments’.
Revolutions in information technology are often accompanied by decades of social unrest. The printing press fomented the religious wars of Europe while also seeding the Enlightenment.
Thomas Rid, the author of Active measures, a critically acclaimed of book on disinformation, stresses that democracy’s approach to truth is so critical that it becomes an existential issue.
Chris Inglis, a former intelligence agent who became the US government’s first national cyber director, offers a compelling take: ‘Diversity beats audacity.’ If truth-seeking is the pillar of democracy, plurality is the glue that holds everything together.
Australia has everything it could ask for: a vibrant, multicultural democracy. Its national security establishment must do everything to preserve that. The discourse on critical infrastructure protection must segue into institutional mechanisms for cognitive security.

