Western Australia’s parliament was hacked last Tuesday with a computer virus forcing the shutdown of its telecommunications systems. According to Speaker Michael Sutherland, the attack impeded a number of house operations including, ‘Hansard publications, the preparation and processing of questions on notice and answers to questions on notice’. Fortunately, the breach didn’t prevent Parliament sitting as usual.
The incident comes following a 2015 audit of sections of the WA government’s digital infrastructure. The assessment found that some agencies didn’t adequately protect information to prevent unauthorised access and data loss. Specifically, it noted the lack of basic controls over passwords, patching, setting of user privileges, copies of sensitive information across systems and poorly configured databases. Cyber security within state governments in Australia often lags behind best practice, but news last week that Queensland is establishing its own cybersecurity unit can be taken as a welcome sign that this trend may soon reversed.
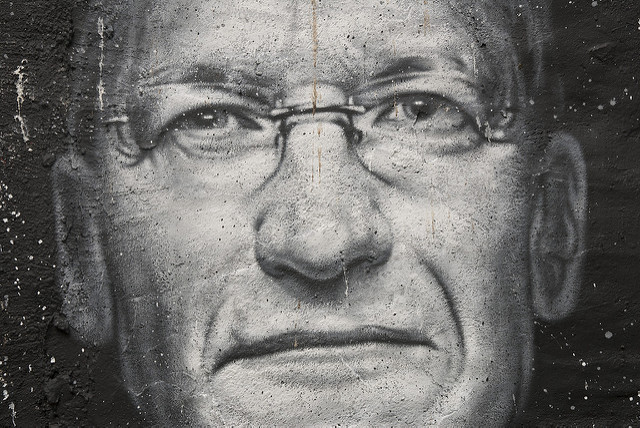
Last week’s ruling that Apple must assist the FBI to unlock an iPhone linked to San Bernardino gunmen Syed Farook has reignited the smouldering discussion on encryption and the difficult balance between privacy and public safety. More public figures have recently come out on one side of the debate or the other. NSA chief Admiral Mike Rogers surprisingly came out on the side of encryption, saying that it’s ‘foundational to the future’, while Microsoft founder Bill Gates has chastised Apple CEO Tim Cook for opposing the court order. Surveys of public opinion in the US have found that there’s a roughly 50/50 split between support for the FBI or Apple. This is significant as Apple will reportedly seek to propel the case out of the courts this week and into the hands of Congress to decide.
Also in the US, the Hollywood Presbyterian Medical Centre in LA has paid 40 bitcoins (equivalent to US$17,000 in ransom to retrieve access to its patient files after a malware attack. The attack prevented access to the computer systems and restricted the ability to share communications electronically, successfully forcing the hospital to return to manual paper and pen patient submissions. Ransomware locks computer systems through file encryption which then demands a ransom payment in exchange for the decryption key.
Japanese companies have been targeted by a highly skilled and well financed state actor according to cyber security firm Cylance. The campaign, named Operation Dust Storm, previously targeted major industry in Japan, South Korea the US, Europe and South East Asia, but has now narrowed its target set to Japanese organisations. The intent of the hackers appears to be long term presence on networks to exfiltrate data, particularly from electricity, oil, gas and transpiration companies. Japan is a frequent target for hackers, however security consultants to Japanese firms and the government continue to highlight weaknesses in corporate culture that views breaches as a loss of face, preventing disclosure and cooperation on common threats.