Cybersecurity continues to be a prominent issue in the US election race. An FBI bulletin, uncovered two weeks ago, reveals that the Bureau has been investigating recent hacking attempts on two state election websites. The hackers, suspected to be agents of a foreign state, targeted voter databases in Arizona and Illinois, accessing up to 200,000 personal voter records.
It’s only been three months since security firm Crowdstrike held two Russian groups responsible for the high-profile hack of the Democratic National Committee (DNC) networks. Wikileaks later published almost 20,000 DNC emails, and Romanian hacker Guccifer 2.0 released DNC opposition research on Trump—both ostensibly obtained from the breach. The incident had a significant impact on the Democratic Party and its convention, and was deemed an act of kompromat—the Russian practice of using compromising information to smear officials and influence events.
Gaining access to voter databases isn’t particularly ground breaking: the information isn’t well protected and some is actually available for purchase from platforms such as NationBuilder.com or VoterRecords.com. But the incident, preceded as it was by the DNC hack the breach of the Democratic Congressional Campaign Committee and a further DNC document dump by Guccifer this week, has intensified concern over of the fragility of computer systems and the interest foreign hackers have in meddling with them.
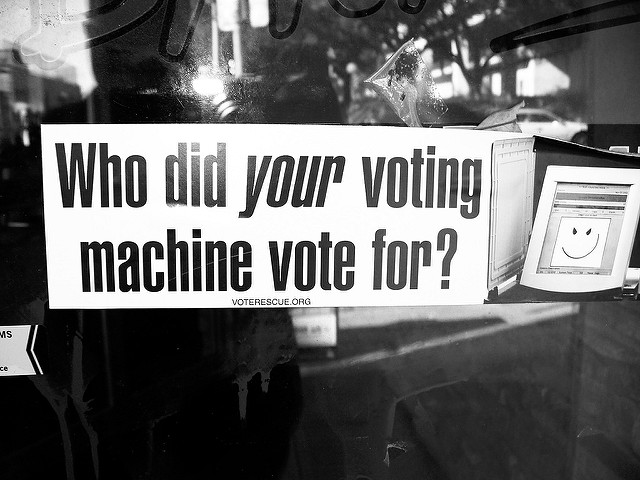
Specifically, there’s concern around the security of the voting machines themselves. Following the troubled 2000 presidential election count, there was a move to modernise parts of the US voting process from paper punching to digital machines. Unfortunately, changes took place without much consideration of security and systems haven’t been diligently upgraded since installation. The Institute for Critical Infrastructure Technology laments (PDF) that as a result, most voting machines are ‘less secure than a modern children’s toy’.
Computer science professor Ed Felten tried to bring attention to this weakness over 10 years ago, successfully installing vote-altering malware to an e-voting machine in such a way that digital forensics would find no trace. Such security flaws remain today, with Felten’s Princeton associate Andrew Appel recently taking only minutes to demonstrate his ability to remodel a voting machine’s circuitry to sabotage vote counting. That same model machine is still used in New Jersey, Virginia, Louisiana and Pennsylvania.
Alternatively, hackers could compromise the voter access card used by citizens to cast their ballot at an e-voting machine. At the Black Hat hacking conference last month, the Symantec stall demonstrated that, if accessed ahead of time, the cards can be reprogrammed to allow an individual to fraudulently submit hundreds of votes at a time.
The integrity of voting data remains vulnerable outside the booth. Hackers could exploit the network connections that communicate the votes to the central database server (where election results are collated), intercepting and modifying the unencrypted data in transit. Or simple manipulation of voter databases, like those accessed in Arizona and Illinois, could lead to targeted disenfranchisement on Election Day, generating panic and a loss of confidence in the process.
While Department of Homeland Security (DHS) Secretary Jeh Johnson maintains that his organisation doesn’t have reason to believe there’s a specific threat posed to the election, he has nonetheless proposed measures to mitigate any risk. DHS has offered to provide states with federal cyber security experts to review voting systems for bugs and vulnerabilities. However such moves have been painted as unconstitutional government overreach and several vital swing-states, such as Georgia and Pennsylvania, declined the offer in favour of reliance on in-house security capabilities.
Generating a tangible impact on an election outcome remains challenging, given the highly decentralised nature of voting networks and the fact that 75% of votes still leave a verifiable paper trail. However, lax cyber security standards could still allow doubt to be cast on an election outcome—a dangerous recipe in a potentially tight race and given Trump’s public conviction that the election is likely to be rigged. Disturbingly, the current system makes it almost impossible to verify the authenticity of the results as 15 out of 50 states don’t create paper voting records in all their jurisdictions, and several states, including Georgia, South Carolina and New Jersey, keep no paper trail of votes whatsoever.
Either way, the high-profile debate around digital voting has certainly highlighted the strategic significance of election systems as national security assets. As Rice professor Dan Wallach advocates, election security is a national security concern. In this vein, Johnson recently suggested digital voting systems be rebranded as critical national infrastructure. Putting election infrastructure in the same category as national power grids and water supply systems would allow DHS to maintain tighter controls and improve the transparency of voting system security, which has been lacking to date.
It’s too late to completely remedy the situation for the 2016 US presidential election, but at a minimum some form of paper trail evidence should be mandated for digital votes. Elevating the security of electoral systems to the federal level may be the only way to enforce a bare minimum security standard before polling day and facilitate more robust risk mitigation into the future.
Debates are underway around the possibility of e-voting in Australia’s next election. These discussions must be informed by an awareness that the ability to secure and corroborate votes is a pre-requisite for going digital. The US experience demonstrates that electronic voting has to be done correctly or not at all, and if it’s pursued, it must be prioritised as an extension of critical national infrastructure.

